Cybersecurity @Melbourne
We are uplifting our capability to prevent, detect, and respond to cyber threats.
What is Cybersecurity?
Cybersecurity is the practice of protecting systems, networks, people, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal processes in our digital world.
Because Cybersecurity threats can impact your studies and personal lives, we need to work together to protect your data, as well as the University.
Cybersecurity at the University of Melbourne
You may not know that in Australia, and globally, tertiary education is one of the sectors most affected by cybercrime.
The University is working to uplift and bolster our current cybersecurity capability to prevent, detect, and respond to cyberthreats. New cybersecurity threats are discovered all the time and as soon as one threat is identified, a new one takes its place.
A cybersecure University of Melbourne is one where we’ve reduced our vulnerability to cyberthreats while balancing our need for openness, autonomy and collaboration. Taking a risk based approach to cybersecurity means we can better balance these needs while still managing our risk exposure.

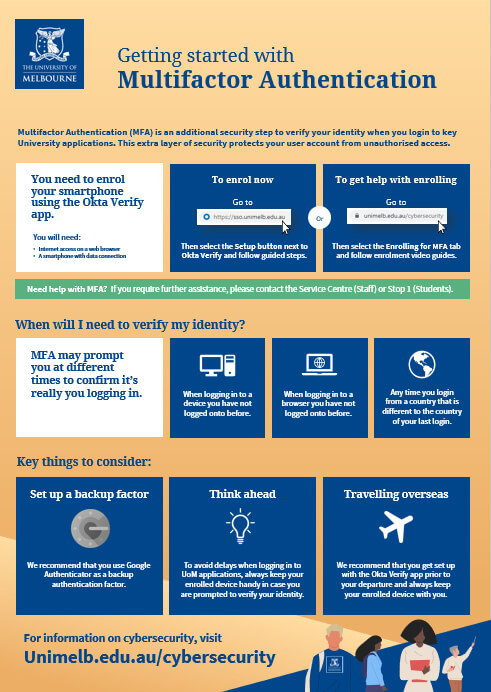
How to enrol your device
You will need:
- Internet access on a web browser.
- A compatible smartphone with data connection and the Okta Verify app installed.
Compatible Smartphone or Tablet Operating Systems
- iOS 13.0+ or iPadOS 13.0+ compatible device
- Android version 7.0+
- Windows Phone version 8.0+
For more information on Multifactor Authentication, visit unimelb.edu.au/cybersecurity.
Have a question?
Visit the Frequently Asked Questions on this page.
Still need help?
To reset or change your factor, see How to reset or change your factor on this page.
You can also call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia), and select option 1 then after entering your Student ID number, follow the prompts to be put through to Student IT for support with Multi-factor Authentication.
For more information on Multifactor Authentication, visit unimelb.edu.au/cybersecurity.
How to reset or change your factor
Have a new mobile device or need to move to a different factor? Here's what you can do!
-
I still have access to my old/existing device or factor
Self-service
- Sign in to the MFA Self-Service page: sso.unimelb.edu.au
- Verify your sign in on your old/existing device.
- Click 'Remove' next to one or all factors linked to your old/existing device.
- You will receive an email notification from the UniMelb SSO System that your MFA Factor has been reset.
- Click 'Set up' next to the factor that you would like to enrol on your new device.
- Follow the set-up instructions that appear on your screen to set up your new factor.
-
I no longer have access to my old/existing device or factor
Student IT Support
- Contact Student IT on 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) by following the prompts (Monday to Friday only).
- If you are unable to contact Student IT via 13MELB or it is a weekend, please start a live chat and inform the Student IT team member that you are unable to call.
- The Student IT team member will assist you with resetting your MFA factor/s.
- You will receive an email notification from the UniMelb SSO System that your MFA Factor has been reset.
- Once reset, re-enrol for MFA using the button below and follow the set-up instructions that appear on your screen.
- Contact Student IT on 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) by following the prompts (Monday to Friday only).
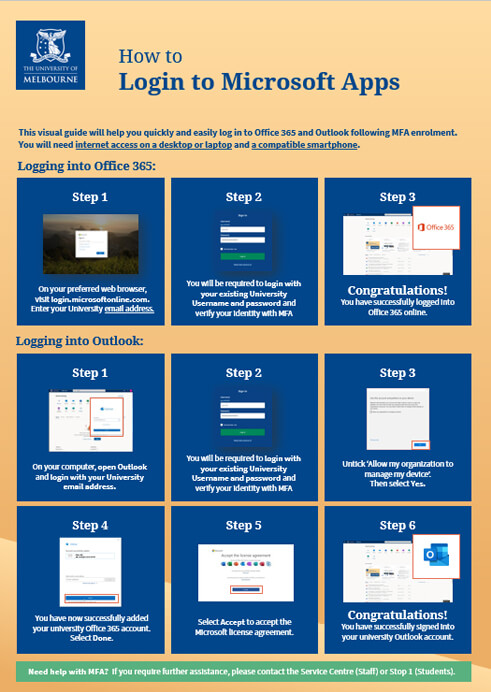
MFA Enrolment Quick Reference Guides
For more information on Multifactor Authentication, please select any of the previews or links below to download a useful visual step-by-step guide:
MFA Enrolment Video Guides
First Time Login
Apple Devices
Android Devices
Enrolling for MFA - Frequently Asked Questions
- What is the Okta Verify app?
A lightweight and secure smartphone application
The Okta Verify app is a lightweight application used to confirm a user’s identity on their smartphone when signing into a key University of Melbourne application. The app is developed by Okta, the University of Melbourne’s technology partner for multifactor authentication (MFA).
Okta Verify provides an additional security step to verify your identity when you login to key University applications. This extra layer of security protects your user account from unauthorised access.
Setting up Okta Verify
The Okta Verify app needs to be downloaded and set up on a compatible smartphone by following a guided process. Once the setup process has completed, the Okta Verify app will display a rolling 6-digit code on your smartphone. At this point you can simply close the app. The use of this code is explained in the next section. You will also receive two emails from Okta confirming your successful enrolment.
Two ways to verify your identity
- Push Notification: When prompted to verify, simply select ‘Yes, it’s me’ on your enrolled smartphone. This requires internet access.
- 6-digit code: Sign into a University application in the normal way and select the ‘or enter code’ option on the Okta Verify prompt screen. Now, open the Okta Verify app on your enrolled device and type the 6-digit code provided into the Okta prompt screen on your web browser, then select ‘Verify’.
The 6-digit code is generated using the industry standard Time-Based One-Time Password Algorithm and is used to authenticate when internet access is unavailable.
Privacy
Okta Verify has passed all required vetting both by the App Store and the University. Okta Verify does not store any personal information – it only requires permission to use your device camera to scan a QR code to register your device with Okta.
For more information, please read the Privacy Collection Notice.
- Where can I download the Okta Verify app?
You can download Okta Verify to your smartphone by visiting your Google store (Android), Apple store (iPhone) and the Microsoft store (Windows). If you are currently in China and using an Android phone, please refer to the FAQ below 'How do I setup MFA from China?'.
Once you have installed the app on your smartphone, please watch our device enrolment video guides to complete your MFA enrolment.
- My smartphone can’t run the Okta Verify app.
If you do not own a compatible smartphone, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- I don’t have a smartphone.
If you do not own a smartphone, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- I don’t want to download the Okta Verify app on my smartphone.
I am concerned about my privacy:
- The Okta Verify App has passed through the App Store and University vetting processes.
- The University has no access to the app on your phone and cannot view any of the data on your phone, other apps installed, monitor calls or track your location
- The app requires internet for push notifications but can also operate offline via the rolling 6-digit code that updates every 30 seconds
- The app does not require you to link it to a particular phone number
I am concerned about using my personal smartphone:
- The University encourages all staff and students to use their personal device to verify their identity
- Providing a University-issued device to each user is not possible due to the high cost
- The security provided by MFA greatly enhances the protection of not just University information but also your personal information
- The use of MFA is a requirement for ongoing access to University services
I am concerned about the performance impact on my smartphone:
- The app uses minimal resources on your smartphone and prompts you only when Okta needs you to verify your current log in
- My location blocks access to the Google Play store. What should I do?
You can manually download and install Okta Verify on your Android smartphone by following these steps:
- On your preferred web browser, go to sso.unimelb.edu.au and login with your University username and password.
- Select the Setup button for Okta Verify in the 'Setup Multifactor Authentication' area. Then select your device type.
- Manually download and install Okta Verify to your smartphone.
Download link: https://uom-share.oss-cn-hangzhou.aliyuncs.com/OktaVerify-6.1.1.apk - On the Setup Okta Verify screen on your web browser, select the 'Can't Scan?' option. Then, from the dropdown menu, select 'Setup manually without push notification'.
- Open the Okta Verify application on your Android device and select Add Account. Then select the 'No Barcode?' option at the bottom of the screen.
- Enter your username and the Secret Key displayed on your web browser. Then select Add Account.
- Select Next on your web browser, then enter the 6-digit code associated with your University account displayed on the Okta Verify application on your Android mobile device. Then select Verify.
- Congratulations! Your account is now registered with Okta Verify. You can now authenticate via the 6-digit codes generated on the Okta Verify application on your Android smartphone.
- Can I use Okta Verify on more than one device?
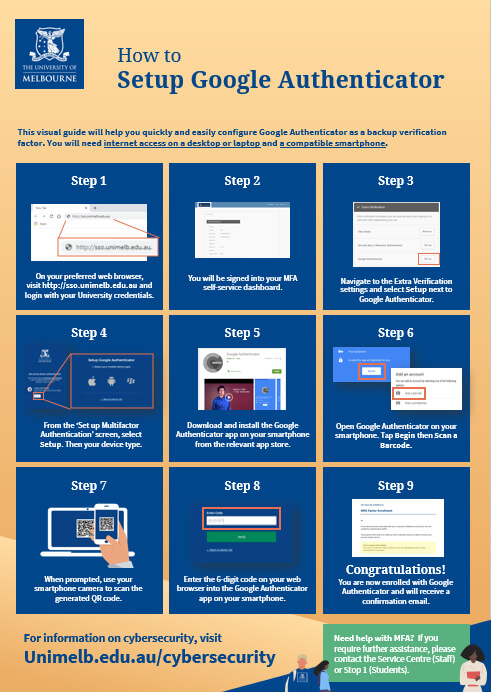
Okta Verify app can only be enrolled on one device, however the University recommends using Google Authenticator as a backup factor.
Google Authenticator can be installed on multiple devices.
- What are the minimum requirements for installing Okta Verify on my smartphone?
Check that your smartphone meets the following requirements:
- iOS 13.0+ or iPadOS 13.0+ compatible device
- Android version 7.0+
- Windows Phone version 8.0+
If you continue to have difficulties, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- I can’t find Okta Verify in my app store.
Please check your smartphone compatibility and ensure your device operating system is up to date:
- iOS 13.0+ or iPadOS 13.0+ compatible device
- Android version 7.0+
- Windows Phone version 8.0+
If you continue to have difficulties, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- When will I be prompted by Okta Verify?
You will be prompted by Okta Verify in the following scenarios
- Whenever you initiate a new browser session or application session in which you haven't previously logged in
- The first time you access your applications from a computer that you have not logged into before
- Any time you login from a country that is different to the country of your last login
If you receive a notification for activity that you don’t recognise, you should contact 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) immediately.
- How can I authenticate using Okta Verify?
- Push Notification –You will be required to verify your identity by accepting ‘Yes, it’s me’ prompt on your smartphone.
- 6 digit code (Offline mode) – Alternatively, you have an option to enter the 6 digit code to verify your identity.
If you require any further assistance, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia).
- Do I need to keep the Okta Verify app on my smartphone, once I have enrolled for MFA?
Yes. In order receive push notifications to confirm your identity, you need to have the app installed on your smartphone. If you have accidentally deleted the Okta Verify app, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
Using MFA - Frequently Asked Questions
- Why is MFA required?
Criminals could steal personal information such as passwords, bank details and date of birth. They could also conduct malicious activities, like unenrolling students from courses and stealing money from bank accounts.
MFA helps keep your personal information and identity protected.
- Can I use Google Authenticator instead?
Yes, however we recommend that you use Okta Verify as your primary authentication factor as you will receive push notifications when verifying your identity.
Once you have enrolled with the Okta Verify app, Google Authenticator will become available to configure as a recommended backup authentication factor.
If you wish to use Google as a primary multifactor authenticator, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- What happens if I delete Okta Verify from my smartphone?
You can use your backup factor, such as Google Authenticator, to enable you to log back in and reset Okta Verify.
If you do not have a backup factor, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- What happens if I get a new smartphone?
- Your old smartphone
- Your new smartphone
- A computer
- On the web browser of your computer, go to sso.unimelb.edu.au, enter your login credentials and click on the 'Send Push' button.
- You will receive a push notification from Okta on your old smartphone. Select ‘Yes, it’s me’ on your old smartphone to verify your identity.
- Once logged in to your account, select the dropdown menu for your account username (located top-right), and select ‘Settings’.
- Under the ‘Extra Verification’ section, select the ‘Remove’ button adjacent to ‘Okta Verify’. You’ll then be asked if you want to revoke your existing Okta Verify token. Click ‘Yes’ to continue.
- You can now follow the steps provided in the How to Enrol for MFA guide to enrol your new smartphone.
- What happens if I forgot my phone?
You are most often only prompted to verify your identity when:
- Logging in to a device you have not logged onto before.
- Logging in to a browser you have not logged onto before.
- Logging in from a country that is different to the country of your last login.
Please continue to access your University of Melbourne applications as normal.
If you are prompted by MFA and have forgotten your smartphone, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- As a student, why am I prompted by MFA on campus?
For improved security, University of Melbourne students are subject to the same MFA standards as staff. This means that, like University staff, you may occasionally be prompted to verify on-campus to further protect your account from unauthorised access.
- Can I get temporary exclusion from Multifactor Authentication?
Multifactor Authentication is required for every University of Melbourne staff member and student.
Temporary exclusion from Multifactor Authentication can only be granted if you temporarily do not have access to your enrolled device and cannot access University applications.
To request temporary exclusion from Multifactor Authentication, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- Okta Verify push notifications and verification codes aren’t working for me?
The most common reason for Okta push notifications and verification codes failing is a mismatch of the time and date settings on your phone and actual location. Please make sure the time and date settings on your enrolled device match those of your current location.
If you are using an Android mobile device, please enable the 'Automatic date and time update' feature in your Settings.On your enrolled device, you can also check the following:
- Push Notifications have been enabled in the Okta Verify app
- Your device operating system is up to date and meets the minimum requirements to support Okta Verify
Please check the above and try again.
For further assistance, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia).
- How do I reset my Multifactor Authentication factor(s)?
If you have access to your enrolled device and need to reset your Okta enrolment, please follow the steps provided in the How to Reset Your Okta Enrolment guide.
If Okta Verify has been deleted and you are unable to reset your factor manually, please visit sso.unimelb.edu.au and authenticate via your backup factor.
If you have trouble resetting any factor, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- What if I can’t have my enrolled device with me?
If you work or study in a restricted environment where mobile devices are not allowed, such as University physical containment rooms or science labs, please call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
- I think my University account may have been compromised. What should I do?
If you encounter suspicious activity on your University account, please immediately call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia) for assistance.
International MFA Access - Frequently Asked Questions
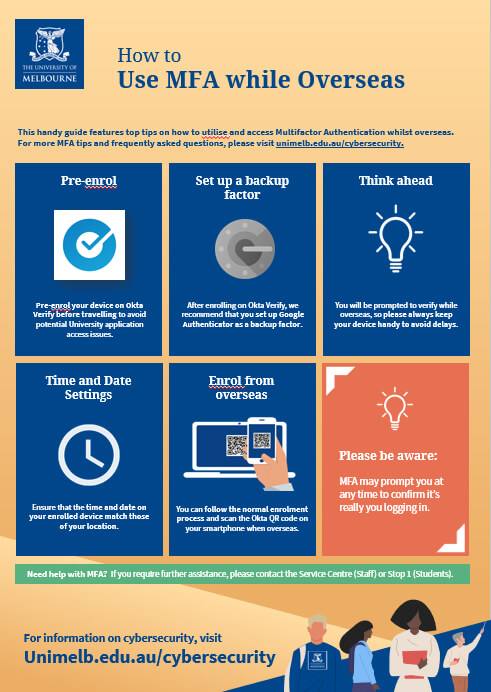
- I will be travelling overseas soon. What should I do before I leave?
Please pre-enrol your device on Okta Verify before travelling to avoid University of Melbourne application access issues.
You will be prompted to verify while overseas, so please keep your device handy at all times to avoid delays.
- Can I use Okta Verify without international data / roaming data?
Yes. You can still verify your identity via access code-based authentication with the Okta Verify app.
If you have internet access on your phone, including through Wi-Fi, you’ll continue to receive Okta push notifications as normal.
- Do I need a SIM card with mobile data?
You only need internet access on your smartphone to receive Okta push notifications.
If you have mobile data, Okta will use your data for push notifications. If not, you can use the access-code based authentication.
Please pre-enrol your device on Okta Verify before travelling to avoid University of Melbourne application access issues.
- Can I enrol from overseas?
Yes. Simply follow the normal enrolment process and scan the Okta QR code on your smartphone when presented.
When enrolling from other countries:
- Ensure that your mobile device has internet access
- If enrolling with a laptop or desktop device, scan the QR code as usual
If enrolling directly with a mobile device (without a laptop or desktop), you will have the following options:
- Send activation link via SMS
- Send activation link via email
- Setup manually without push notification
The University recommends that you use the "Send activation link via email".
SMS links may not be delivered or may result in roaming fees (depending on your mobile plan).
Setting up manually is not recommended - you will need to enrol again to start receiving push notifications.
For further assistance, please call +61 3 9035 5511.
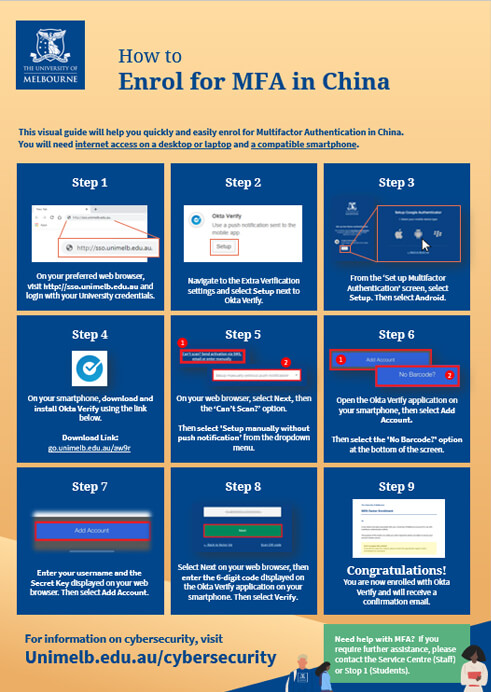
- How do I setup MFA from China?
Due to the restrictions on Google services in China, you won't be able to download and install applications such as Okta Verify or Google Authenticator from the Google Play Store on Android devices.
You can manually download and install Okta Verify on your Android smartphone by following these steps:
- On your preferred web browser, go to sso.unimelb.edu.au and login with your University username and password.
- Select the Setup button for Okta Verify in the 'Setup Multifactor Authentication' area. Then select your device type.
- Manually download and install Okta Verify to your smartphone.
Download link: https://uom-share.oss-cn-hangzhou.aliyuncs.com/OktaVerify-6.1.1.apk - On the Setup Okta Verify screen on your web browser, select the 'Can't Scan?' option. Then, from the dropdown menu, select 'Setup manually without push notification'.
- Open the Okta Verify application on your Android device and select Add Account. Then select the 'No Barcode?' option at the bottom of the screen.
- Enter your username and the Secret Key displayed on your web browser. Then select Add Account.
- Select Next on your web browser, then enter the 6-digit code associated with your University account displayed on the Okta Verify application on your Android mobile device. Then select Verify.
- Congratulations! Your account is now registered with Okta Verify. You can now authenticate via the 6-digit codes generated on the Okta Verify application on your Android smartphone.
For further assistance, please call +61 3 9035 5511.
MFA Support
Need help with MFA?
Call 13MELB (13 6352 - within Australia, +61 3 9035 5511 - outside Australia), and select option 1 then after entering your Student ID number, follow the prompts to be put through to Student IT for support with Multi-factor Authentication.
Do you have a question about MFA?
Refer to the MFA Support & FAQ page for frequently asked questions and advice on configuring and managing Multifactor Authentication.

LastPass helps you generate and manage strong, unique passwords, then keep them safe. The University of Melbourne has partnered with LastPass, providing all students with LastPass Premium, at no cost.
How does LastPass work?
LastPass offers a browser extension and standalone application, either of which you can use to save and access all your passwords. After you download LastPass, you’ll find the LastPass button in your browser toolbar where you will login to LastPass every day.
Benefits of LastPass
LastPass stores your confidential and private information in the secure 'Vault', making it easier for you to store all your important information in one place. Some key benefits of using LastPass are given below:
- Generating unique and strong passwords
- Securely share passwords and notes if you choose
- Auto-fill forms for addresses and credit card details
- Safely store digital records
LastPass FAQs
-
How secure are passwords with LastPass?
The information in your LastPass Vault is protected by client side encryption and is sent to and stored by LastPass encrypted. This means only you can decrypt and access your data. For more information on LastPass encryption and security refer to the LastPass Technical Whitepaper.
-
What if I already have a LastPass account?
If you have a LastPass Free account, you can upgrade to a LastPass Premium account, at no cost.
If you have a current LastPass Premium account, you can transfer your account under the UoM licence and we will cover the costs for you as long as you are a current staff or student.
Please note that you would be required to redeem your UoM Premium licence subscription after disabling the Auto Renew subscription from your LastPass Premium account settings.
Learn more about disabling Auto Renew on your account.
-
What happens if I forget my master password for my Premium account?
We recommend you set up the SMS account recovery option to help regain access to your account, should you forget the master password.
In any case, if you forget your master password, see this LastPass support page. Please note that neither LastPass support nor Student IT are able to reset your password on your behalf.
-
Will I have access to my LastPass account if I leave the University?
Staff and students will still be able to enjoy the benefits of a having a Premium licence for a period of one year after leaving the University. Once this year has passed, their Premium account will revert to LastPass Free.
-
Where can I go to for support with LastPass?
Support for LastPass Premium is provided completely through LastPass. If any issues arise, please look at the LastPass Knowledge Centre.
-
What operating systems does LastPass support?
The LastPass browser extension supports the following operating systems:
- Windows 8.1 and newer
- macOS 10.14 and newer
- Linux
- Chrome OS
-
What web browsers does LastPass support?
- Google Chrome
- Mozilla Firefox
- Microsoft Edge (including Legacy version)
- Apple Safari
- Opera
To check if LastPass will work on your device, please visit their system requirements page.

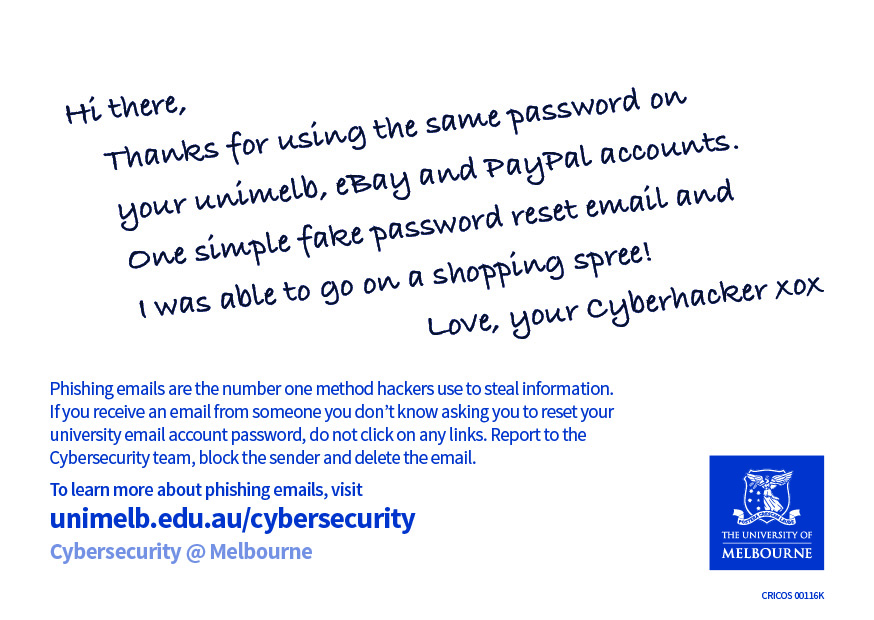
Top Tip: Be wary of Phishing Emails!
Phishing emails are the number one method hackers use to steal information. If you recieve an email from someone you don't know asking you to reset your university email account password, do not click on any links. Report it to the cybersecurity team, block the sender, and delete the email
Contact spam-report@unimelb.edu.au to report any suspicious behaviour.Tips for keeping your devices safe
Cybersecurity threats are becoming more advanced so it’s important to learn how to identify the risks and take steps to safeguard your devices and information. The loss or theft of information can cause personal inconvenience and have financial and other consequences.
- Connect securely
Random wireless hotspots can steal your passwords and private information. It is even possible to set up a hotspot that looks legitimate but lets people spy on everything you do while connected. To protect your privacy, use ‘UniWireless’ where available. Use the Virtual Private Network (VPN) when connecting from public wireless to remotely access the campus computer or if you need to transfer data securely to the University’s network.
- Keep your computer and phone software updated
The best way to protect yourself is to keep your computer and mobile phone operating systems and all your applications up-to-date. Make sure you have auto-updates turned on where it is available. Updating your software removes weaknesses that might be exploited by an attacker.
- Backup
Make extra copies of your important files such as assignments and store them in a separate location like cloud storage, file servers, external hard drives, or USB memory sticks.
- Lock your devices
Always remember to lock your computer or phone screen before leaving it unattended. In addition, set your device to auto-lock after a period of inactivity (e.g. 5 minutes) in case you forget to lock your screen. This minimises the opportunity for someone to gain unauthorised access to your device. If you leave your device unattended, also be mindful of the potential for theft.
- Lost or stolen data and devices
Following these tips reduces the risk of someone breaking into your device and harvesting your data.
Changing all your passwords as soon as you realise your device is missing helps to further protect you.
Reporting that your device may be vulnerable also helps, especially if it wasn’t protected. Remember to contact your financial and other service providers as well as the University (by logging a ticket in ServiceNow), family and friends.
- Select a strong password
Research into choosing the best password is continually evolving our thinking around passwords, but the overarching principle is that your password should be easy for your to remember but hard for someone else to guess.
We recommend using a passphrase, which is 2 or 3 unrelated words joined together that also incorporates some numbers and symbols. It is also essential that you don’t reuse the same password for multiple accounts.
The current minimum requirements for your UniMelb password are that it:
- Must contain at least 8 characters
- Must contain at least one numeric character (0-9) and once special character (e.g. !, #, @)
- Must not be one of the last 10 passwords used
- Must not contain First Name, Last Name and UserID
- Don’t reuse passwords for different accounts
Use a different password for each account and website that you use. This ensures that even if one system is compromised, it won’t give automatic access to your other accounts. Having different, as well as complex, passwords will help to ensure your data and identity is protected.
- Consider using a firewall
A firewall helps you specify which other computers on the network your computer may communicate with. This will avoid unsolicited connections to your computer. A firewall can also be configured to request for your permission before allowing applications to access the network or Internet. There are free software firewalls available for download via the Internet. A firewall is particularly recommended for network or Internet connections that are active for long periods of time, for example, broadband Internet connections or wireless networks.
- Install and update anti-malware software
Anti-malware software (sometimes referred to as anti-virus) helps detect, block and remove malicious software from your computer, keeping your sensitive information safe. Devices owned by the University of Melbourne will automatically have this software installed and updated. Use reputable anti-virus software on your personal devices and ensure it is regularly updated. Configure it to scan every file accessed through any source, e.g. email, Internet, and disks. Occasionally, scan all disks for viruses and corrupt files. The University may notify you if your computer has been detected to contain malware.
- Internet Privacy
A good rule of thumb is to only post information you would be willing to put on a banner in a public place.
Assume that any information you enter online is public unless you are using a known, trusted, secure site.
Social networking sites (e.g. Facebook, Twitter), personal web pages, and blogs are great places for people to find personal information about you and once you post something, you can't take it back.
- Be cautious about downloads
Only execute or download files to your computer that are from known and trustworthy sources, as anti-virus software is not foolproof. Do not open email attachments in unsolicited emails and be wary of unsolicited emails requesting information or inviting you to click on a link.
- Minimise storage of sensitive information
Delete sensitive information whenever you can. Keep it off of your workstation, laptop computer, and other electronic devices if at all possible.
Don't keep sensitive information or your only copy of critical data, projects or files on portable or mobile devices (such as laptop computers, tablets, phones and memory sticks) unless they are properly protected. These items are extra vulnerable to theft or loss.
- Watch out for phishing or suspicious emails
You need to be increasingly cautious of unsolicited or suspicious emails, as they aim to steal your electronic identity and use it to compromise your personal information or access your computer system. Continue reading about unwanted emails.
Top Tip: Avoid using the same password across websites
Use a different password for each account and website that you use. This ensures that even if one system is compromised, it won’t give automatic access to your other accounts.
Having different, as well as complex, passwords will help to ensure your data and identity is protected.

- Report suspicious activity
Notify the University of Melbourne Cybersecurity team of any suspect or unusual behaviour via:
Report Activity
spam-report@unimelb.edu.au. - Have you been affected by a cyberthreat?
If you suspect that you have been the target of cyberthreat, please lodge a ticket through Service Now for assistance with moving forward to protect yourself and your device.
Log a Ticket
 Getting Started
Getting Started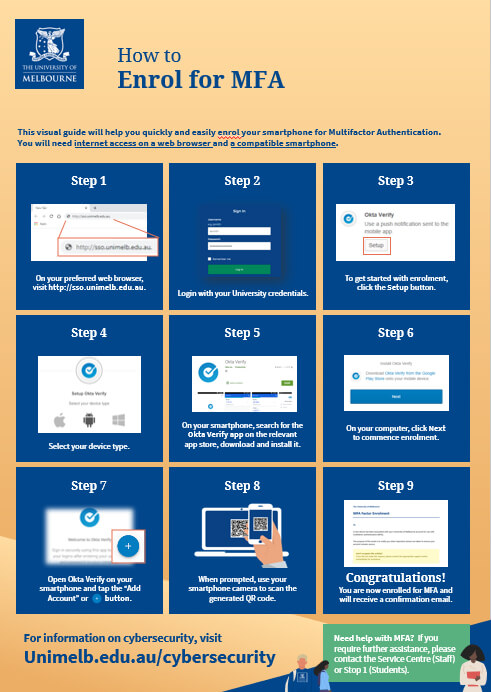 How to
How to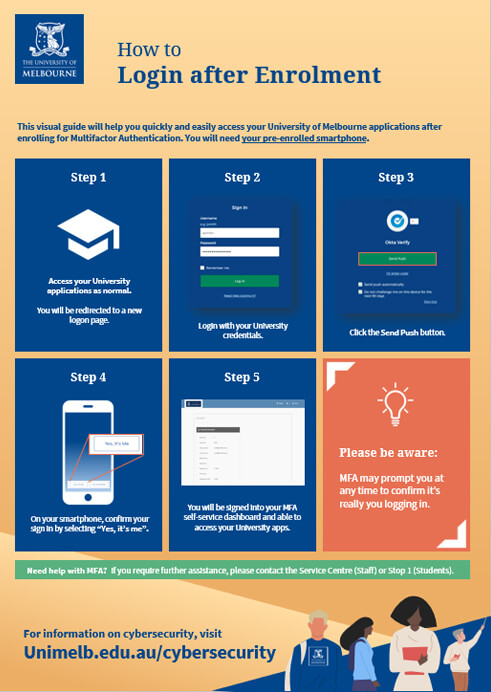 How to
How to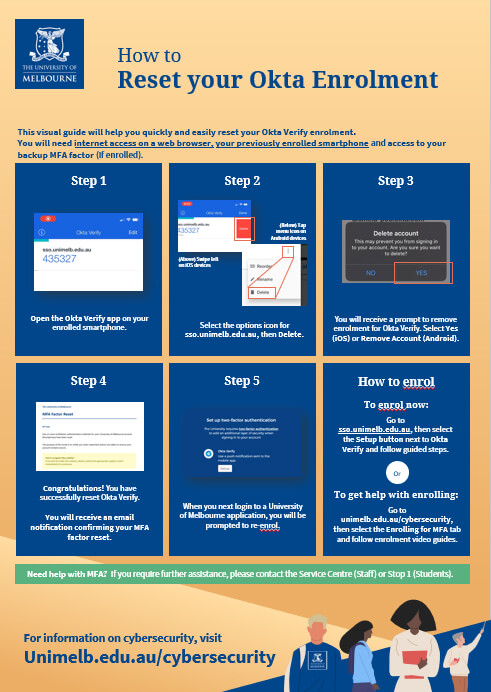
 How to Setup
How to Setup